Glossary
Automated License Plate Reader (ALPR)

Fixed and mobile automated license plate readers. Photo by Mike Katz-Lacabe (CC-BY)
Automated license plate readers are cameras attached to fixed locations or to patrol cars that capture every license plate that passes. The data is uploaded to searchable databases with the time, date, and GPS coordinates.
Body-Worn Camera (BWC)

Axon body-worn cameras. Source: Tombstone Marshal's Office
Many law enforcement agencies require officers to attach body-worn cameras to their chests or shoulders to capture interactions with suspects and the public. Some cameras stream live and can be combined with face recognition technology.
Camera Registry

Some law enforcement agencies ask residents and businesses to voluntarily provide information about the security cameras they have installed on their properties. This is usually called a camera registry, and it is often integrated into other software packages, such as Motorola Solutions’ CityProtect suite.
Cell-Site Simulator (CSS)

A Harris Corporation Stingray II. Source: USPTO Records
Cell-site simulators, also known as Stingrays or IMSI catchers, are devices that masquerade as legitimate cell-phone towers, tricking phones within a certain radius into connecting to the device rather than a tower.
Crowdsourcing
Crowdsourcing is a research technique that involves recruiting a large number of people, such as students, members of your supporter base or readership, to collaborate on a single project.
Drone (UAV)

Drones are also known as unmanned aerial vehicles. Police remotely control these devices to surveil crowds from above or locations that would otherwise be difficult or dangerous to observe by a human on the ground.
Face Recognition (FR)

Face recognition is a method of identifying or verifying the identity of an individual using their face. Face recognition systems can be used to identify people in photos, video, or in real-time. Law enforcement may also use mobile face recognition devices to identify people during police stops.
Fusion Center
Fusion Centers are intelligence hubs and command centers that enable intelligence sharing between local, state, tribal, territorial, and federal agencies, with a focus on homeland security matters. These are part of a national fusion center system supported by the U.S. Department of Homeland Security.
Gunshot Detection

Gunshot detection is a technology law enforcement uses to receive alerts on where gunfire may occur in neighborhoods. This technology relies on a series of acoustic sensors mounted on street lights or on the sides of buildings. When a loud noise triggers the sensors, software triangulates the estimated location of the gunfire.
Open-Source Intelligence
Open-source intelligence, or OSINT, is a term used to describe gathering information that already exists online—from news stories, social media posts, press releases, or documents buried in government websites, often turned up through using advanced search engine techniques.
Predictive Policing
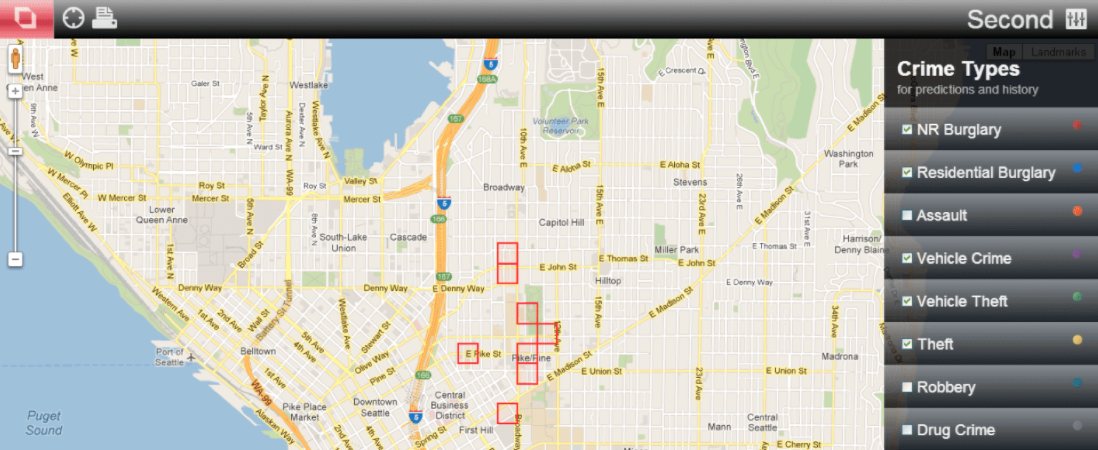
Predictive policing is software used by law enforcement to select neighborhoods or blocks where they should focus resources or to identify individuals for investigation. Law enforcement feed records and data—such as police stops or calls for service—into the algorithms, which vendors say can predict where crime is likely to occur.
Real-Time Crime Center (RTCC)

Fresno Real-Time Crime Center. Source: Fresno Police Department
Real-Time Crime Centers are hubs where police ingest and analyze surveillance, intelligence, and data from a number of sources in real-time. RTCCs are often equipped with walls of monitors with live feeds from camera networks. Analysts are often able to access a wide variety of surveillance technologies, including automated license plate readers, gunshot detection, predictive policing, and face recognition. Unlike fusion centers, RTCCs tend to be focused on local level activities and a broader range of criminal investigations.
Ring/Neighbors Partnership

Ring Inc., a subsidiary of Amazon, markets “doorbell cameras” and other home surveillance devices to residents. Ring also operates a social media platform, Neighbors, which encourages residents to share video footage and incident reports with other residents and the police. Ring has signed agreements with more than 1,300 law enforcement agencies to promote its products.
Video Analytics/Computer Vision
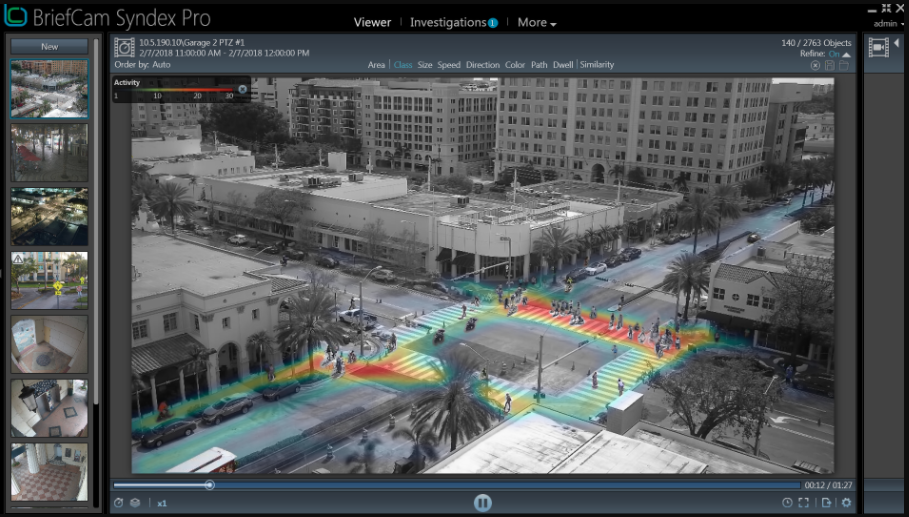
Video analytics and computer vision are terms that surveillance companies use to describe advanced software applied to video feeds to identify the movements of people and objects and detect patterns and anomalies. It is often coupled with artificial intelligence/machine learning and face recognition technology.